Building a Resilient Payout System with an API
Introduction: Inbound is Easy, Outbound is Dangerous
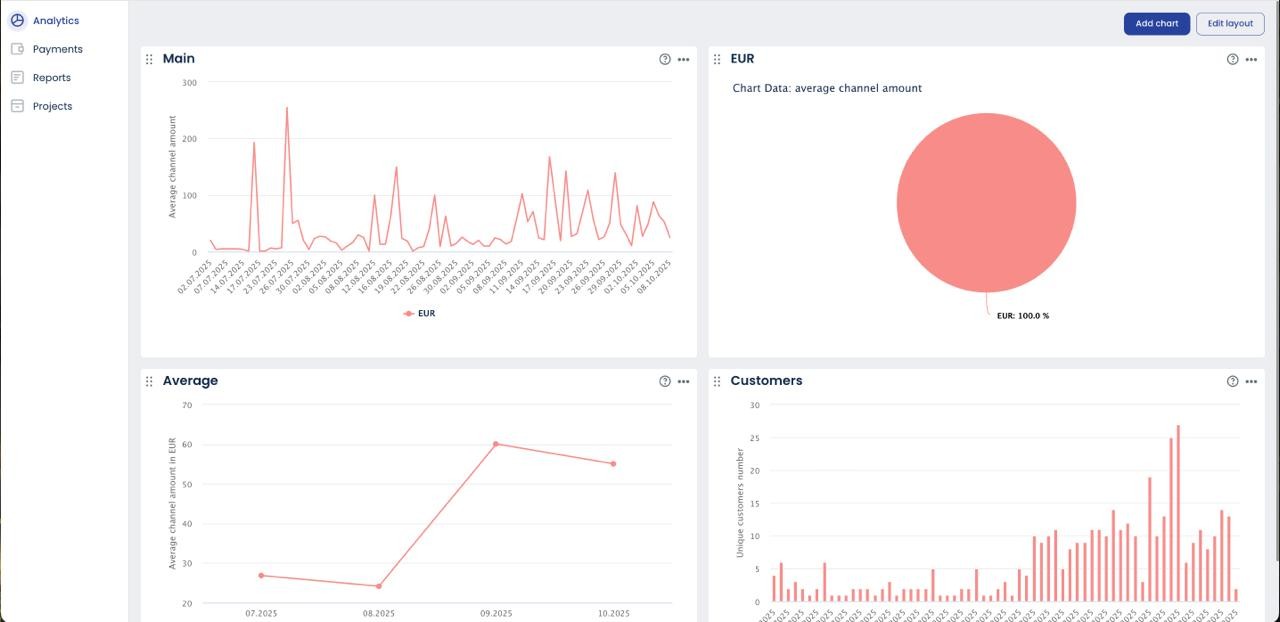
We spend most of our time optimizing inbound payments for acceptance, treating every decline as a potential lost sale. That is a problem of revenue maximization. Payouts are a problem of capital control. A failed deposit is an opportunity cost; a failed outbound transfer—a duplicate payment, a transaction sent to the wrong beneficiary, or a compromised API key that drains an account—is an irreversible financial loss. This fundamental distinction must drive every decision in your system architecture. While pay-in APIs are built for flexibility and conversion, a payout API integration must be engineered for absolute precision and security. The primary goal is not speed, but financial loss prevention and auditability. Architecting for outbound money movement requires a defensive, zero-trust mindset, where every request is treated as a potential vector for catastrophic failure. For a review of foundational principles that apply here, see our guide on secure gateway integration.
Architectural Patterns: Queues and Batching
A synchronous architecture—where a user action directly triggers a live call to the payout API—is an unacceptable liability. Tying a user session to the high latency and potential failures of external banking networks creates a brittle system that cannot scale or recover gracefully. The only robust architecture for a payout API is a decoupled one, built on a foundation of message queues.
The correct workflow is straightforward: the user-facing application does not call the gateway directly. Instead, it publishes a payout instruction to a queueing system like RabbitMQ or Kafka. This provides immediate feedback to the user and ensures the request is durably stored. A separate, isolated pool of workers consumes from this queue, managing the state machine, API calls, and retry logic.
This decoupled model allows you to automate payouts using two distinct strategies:
- Real-Time Processing: For use cases like iGaming or crypto withdrawals where speed is a product feature, workers process messages from the queue as they arrive.
- Batch Processing: For predictable, non-urgent flows like affiliate commissions or supplier payments, a scheduled job can pull a batch of pending payouts from the queue. This batch processing approach is superior for minimizing transaction fees on traditional banking rails and reducing API call volume.
Liquidity Management: Pre-Funding and Balance Checks
Payout APIs do not draw directly from a corporate bank account; they debit a pre-funding wallet that you must keep capitalized. This operational float is a common point of failure. Running this balance to zero results in rejected payouts and a compromised user experience. Robust balance management is therefore not an accounting task, but a core engineering responsibility that must be automated.
The sequence of operations must be atomic and strictly enforced to prevent race conditions. Before initiating any payment, your system must:
- Check Available Balance: Execute a GET request to the gateway’s balance endpoint.
- Reserve Funds Internally: If the balance is sufficient, immediately place a hold or lock on the payout amount in your own database. This prevents a second, concurrent process from allocating the same funds.
- Execute Payout: Only after the internal lock is successful, send the POST request to the gateway.
- Reconcile: On confirmation, deduct the reserved amount. If the payout fails, release the lock.
Automated alerting that triggers when your float drops below a set threshold is a non-negotiable operational control.
Security: Hardening the Outbound Pipe
A payout API endpoint is a direct conduit to your treasury; securing it is an exercise in asset protection, not just IT security. Compromise is not a data breach, it’s a cash event. The following controls are not optional best practices; they are the minimum required layers to operate a mass payment API responsibly.
- Strict IP Whitelisting: This is the most fundamental control. The ability to call the payout endpoint must be restricted at the gateway level to a specific, hardened set of your production server IP addresses. There are zero valid use cases for allowing payout requests from an unknown origin. Failure to enforce strict IP whitelisting is gross negligence.
- Segregated API Credentials: Never use the same API key for pay-ins and payouts. Payout credentials must be distinct, with their scope limited exclusively to withdrawal functions. This mitigates the risk of a compromised read-only or deposit key being escalated to execute unauthorized payments, aligning with the principle of least privilege.
- Automated Velocity Limits: You must implement circuit breakers. These are not simple rate limits; they are business logic rules that monitor outflow. For example, if total payout volume exceeds a set threshold within a given hour, the system should automatically halt all further transactions pending manual review. These velocity limits are your primary defense against automated drain attacks initiated by a compromised key or a rogue internal script.
Handling State: The Asynchronous Reality
The most dangerous assumption an engineering team can make is equating a 200 OK from the payout API with a successful transfer of funds. This response does not mean money has moved; it means the gateway has successfully accepted your instruction. The transaction now enters an asynchronous, multi-stage lifecycle dictated by external banking and settlement networks that operate on their own timelines. Your system’s state machine must reflect this reality.
The only source of truth for a payout’s final status is the webhook. Relying on API polling is inefficient and misses the fundamental event-driven nature of payments. Your architecture must be built around a listener that processes status updates, making webhook reconciliation a core competency. When a payout_failed event is received, your system must trigger an automated and idempotent job to credit the funds back to the user’s internal wallet. Handling payment failures gracefully is paramount for maintaining ledger integrity and user trust. Conversely, a payout_succeeded event is the final, immutable confirmation. As an example, the process flows and webhook payloads are detailed in resources like the OpenPayze Payout Documentation. This asynchronous model is especially critical in verticals that depend on high-volume, automated disbursements, such as those discussed in our brief on Payout Solutions for iGaming and Forex Affiliates.
Conclusion: Automate but Verify
The architectural mandate for outbound payments is clear: decouple the instruction from the execution, queue every request for durable processing, and verify every final state asynchronously via webhooks. A resilient system is not one that never fails, but one that anticipates failure and contains the financial and operational fallout by design. This approach transforms the process from a brittle, real-time risk into a controlled, auditable workflow. For engineering teams tasked with building a mass payment engine, the path begins with a scalable infrastructure and rigorous developer documentation. Sola’s payout API provides the foundation for constructing a system with the required security and control primitives built in from the very first line of code.